Are Your Document Scanning Workflows Secure?
For businesses that work with sensitive information, security is a critical factor when choosing the best document scanning solution.
Document scanners provide an efficient way to convert analog information into electronic format for storage and data processing. For businesses that work with sensitive information, security is a critical factor when choosing the best document scanning solution.
How Document Scanners Handle Data
Most document scanners contain both nonvolatile storage (NVRAM) and volatile memory (SDRAM). Nonvolatile memory stores program data, scanner settings, and calibration data. The data from scanned documents is stored in volatile memory. On most scanners, the information in volatile memory is deleted as soon as it’s delivered to its destination, or when the device is switched off.
However, scanners in many multi-function printers (MFPs) often retain scanned image data, which can introduce serious information security risk.
Scanners from Kodak Alaris do not store any data. Instead, the data from scanned documents is typically transferred directly to a computer, which has its own process for storing information. It’s important to ensure that the computer you connect to a scanner conforms to your organization’s information security policies.
Scanner Features That Protect Data Security
In the process of converting information from sources like paper forms, contracts, identification documents and so forth, the data path from the scanner to its storage location must be secure, in addition to the storage location itself.
Here are some standard technologies and methods that help reduce risk and ensure the security of your digital transformation path:
-
Remote key entry: This measure prevents full image exposure to human eyes; operators can only see individual lines of data rather than an entire scanned document.
-
Limited designations: Limited designations prevent data theft by PC and MFP operators. You can configure a document scanner to scan only specific areas of a document and permanently delete data once it’s sent to its destination.
-
Optical Character Recognition (OCR): OCR identifies information on a document and converts it into readable digital data. OCR precludes the need for human eyes to see sensitive information before it’s delivered to its destination.
-
Encryption: Encryption limits access to scanned and stored data. A combination of secure passwords and Transport Layer Security (TLS) encryption can prevent data from being compromised.
-
Redaction: Redaction plays an important a role in secure document scanning. The process restricts access to sensitive information to authorized users only.
Kodak Alaris: Going Further to Protect Information
In addition to using TLS encryption to secure the network data path from the scanner into your enterprise system, scanners from Kodak Alaris go beyond standard security measures to help protect critical business information.
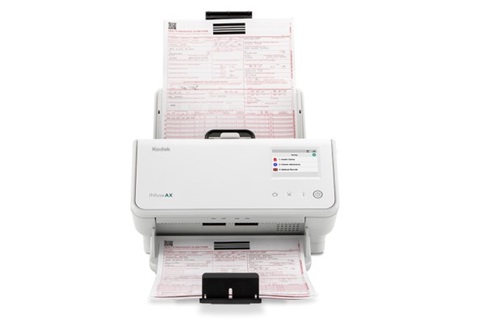
For example, many scanners from Kodak Alaris use a secure boot process that validates “trusted” firmware before executing, thus eliminating a potential security vector. In addition, the INfuse Smart Connected Scanning Solution does not require a connected PC, and you can enforce user authentication at the device to prevent unauthorized use and minimize risk.
Reduce Risk by Eliminating the Connected PC
In their 2021 global report, IBM reported the average cost of a data breach now exceeds $4 million. A significant percentage of corporate security events are being traced to attack vectors like phishing emails and web pages. As a result, security professionals are increasingly deploying solutions that do not rely on attached PCs, which are highly vulnerable to malware, API breaches, and unauthorized use.
To help reduce risk to your business, you can eliminate the PC from your document scanning environment and digitization workflows. The INfuse Solution does not require a PC, so you can confidently and securely scan information directly into your business systems for immediate action.
User Authentication at the Device
INfuse is a trusted network scanning solution that integrates with business applications via plug-in modules and APIs to enable fast and secure conversion of documents into digital data. This is critical in many business contexts, such as accounts payable processing and medical record management.
In 2021, Kodak Alaris released several expansion modules for INfuse, including support for HID OMNIKEY Smart Card Reader to ensure fast user authentication. This protects scanners from unauthorized use and provides an extra layer of security when scanning documents that contain sensitive information. Authorized employees simply swipe their ID badge on an INfuse AX Scanner to quickly authenticate and begin scanning.
Secure Data Storage
There are four direct-to-destination connector modules that enable INFuse AX scanners to send converted document data directly to a preferred repository:
-
Tencent COS Connector Module
-
Microsoft Azure Blob storage
-
Alibaba OSS Connector Module
-
Amazon S3 storage
These direct-to-destination modules save time, improve security, eliminate maintenance issues and delays, and reduce the overall operational costs of document scanning.
Let us help you transform your document capture workflows and put your data to work. Contact us via the form below and we’ll get started together.
Insights and Case Studies
Kodak Alaris’ INfuse Smart Connected Scanning Solution enables Xenith’s Scan@Home Solution
To help businesses scan documents remotely, Xenith Intelligent Workplace Services partnered with Kodak Alaris to set up a smart Scan@Home Solution that integrates directly into line of business systems.
INfusing Innovation into Network Scanning
By Ralph Gammon, Editor, Document Imaging ReportThe new INfuse Smart Connected Scanning Solution from Kodak Alaris leverages Kodak S2000 Series Scanners and INfuse Management Software to scan-enable third-party applications in an efficient and secure manner.
Related Challenges
ABOUT THE ALARIS DIVISION OF KODAK ALARIS
Kodak Alaris is a leading provider of information capture and intelligent document processing solutions that simplify business processes. We exist to help the world make sense of information with smart, connected solutions powered by decades of image science innovation. Our award-winning software, scanners, and professional services are available worldwide and through our network of channel partners.
Partners
Privacy Notice | Legal / Site Terms | California Notice at Collection | Do Not Share My Personal Information
© 2024 Kodak Alaris Inc. TM/MC/MR: Alaris, ScanMate. All trademarks and trade names used are property of their respective holders. The Kodak trademark and trade dress are used under license from Eastman Kodak Company.